Nobody told me I was going to run a podcast. Which is usually how the work that teaches you the most begins. One week I was writing cybersecurity…

I killed my old Kindle recently. It stopped holding a charge the way it used to, the way old things quietly stop doing what they were made for…
I have been using AI almost every day for the better part of two years. I build things with it. I think alongside it. I have written at…
Last week I told you about the detours. The data centers, the asphalt, the Korean boss, the slow climb back to marketing. This week, I tell you what…
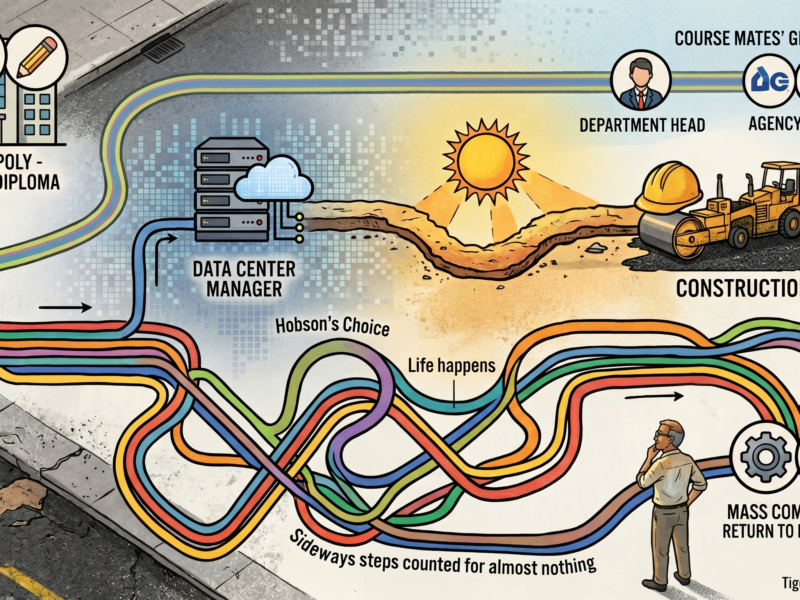
From managing data centers to paving roads under the merciless sun, my career path has been anything but a straight line. Discover how a decade in construction and a detour through the dot-com bubble taught me lessons you will never find in a marketing textbook, and why every sideways step was actually preparation for the AI era.

Cybersecurity is too vast and dynamic for anyone to tackle alone. Learn why veteran consultant Emil Tan believes that joining a community is the ultimate game-changer for your career, offering everything from accelerated learning and mentorship to the resilience needed to avoid burnout in a high-pressure field.
Penetration testing, security operations, or compliance? The cybersecurity industry offers countless paths, but choosing the wrong one can lead to unnecessary detours. Explore expert advice from Mike Lo on how to assess your strengths, set clear milestones, and find the perfect niche before you take your next career step.

In a field where attackers are constantly innovating, standing still means falling behind. Discover why continuous learning is non-negotiable in cybersecurity, and learn practical strategies to overcome information overload, beat imposter syndrome, and build a sustainable learning habit that keeps you one step ahead.
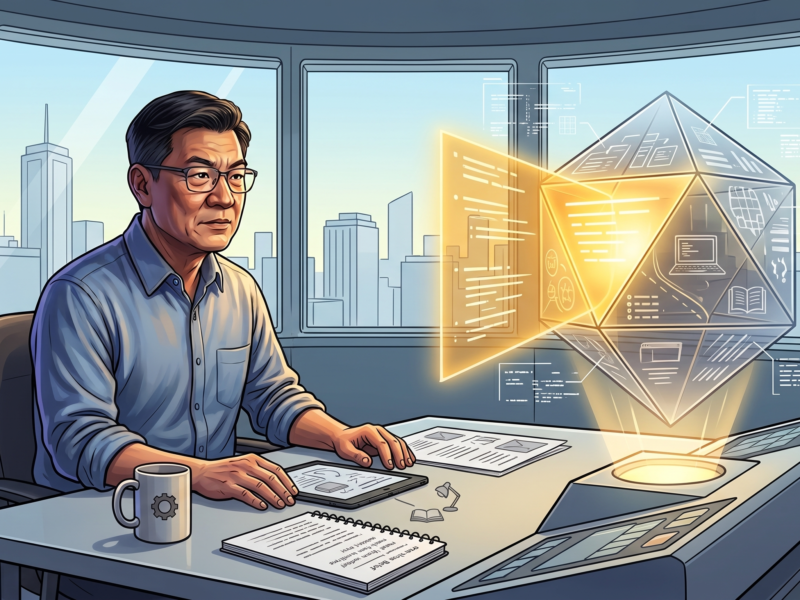
Artificial Intelligence is no longer just a buzzword; it is fundamentally rewriting the security playbook. Join Faisal Yahya as we explore how AI and Machine Learning are transforming threat detection from reactive to proactive, and uncover the actionable steps you need to implement these powerful tools without falling into common traps.